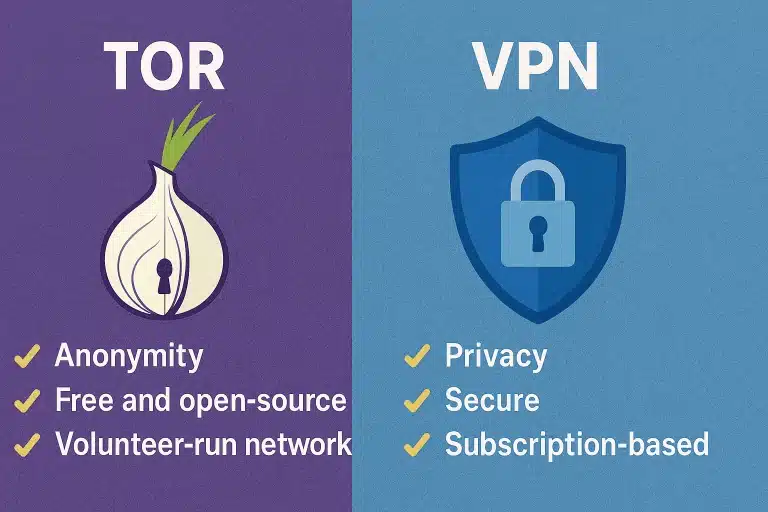
A VPN, which stands for “Virtual Private Network,” is one of the many different methods available that can utilize WiFi hotspots and the internet itself by adding privacy and security features to both public and private networks. There is a number of corporations who invest in the services of VPNs in order to successfully protect confidential and sensitive data; however, nowadays, many individuals have taken to using personal VPNs now that one-on-one interactions are taking place more on the internet rather than in person.
Regardless, a VPN brings an increased amount of privacy because it replaces the typical IP address with one from the VPN provider, which is a service that virtually anyone can take advantage of anywhere in the world as long as the VPN provider offers service in a particular city. For instance, an individual can obtain a VPN that originates from New York even though they actually live in California.
VPN SECURITY
As previously mentioned, there are a number of corporations who invest in VPNs due to the overwhelming amount of security that they provide in terms of keeping certain information completely safe. Unfortunately, there are quite a few easy ways to intercept information that is being sent across a network, with Firesheep and WiFi spoofing being the two top ones. While a firewall can protect your information on a computer itself, a VPN goes much further by protecting your information across the entire web. This is due largely in part to VPNs utilizing both secure tunneling techniques and advanced encryption protocols to completely surround each and every single data transfer.
VPNs are further essential due to the fact that security threats are always evolving and people are relying more and more on the internet every day. Integrity checks are also performed in order to ensure that the connection itself has not been hijacked by any outside source and that any data has not been lost.
SETTING UP A VPN
The process of actually setting up a VPN is rather straightforward and simple, just like entering a username and/or server address. VPNs can be configured by smartphones by using PPTP and L2TP/IPsec protocols. In addition, PPTP VPN connections can be figured by practically every major operating systems. However, anyone wishing to utilize OpenVPN and L2TP/IPsec protocols must have a small open source application and a certificate download.
VPN Protocols
Below is a list of some of the most common protocols associated with VPNs:
- PPTP: This protocol has existed ever since Microsoft Windows 95 was first launched. Perhaps the most popular aspect of this particular protocol is that it can be set up on essentially every major operating system; however, PPTP’s security has often been called into question since it is not the most secure, but strong at the same time.
- L2TP/IPsec: This protocol is known to be stronger than PPTP and contains more features. L2TP/IPsec essentially implements two different protocols together and uses only the best features from each one, which makes the L2TP portion able to create a tunnel, while the IPsec portion provides a channel that is secure.
- OpenVPN: This protocol is SSL-based and one that also continues to gain popularity amongst many individuals. This particular protocol is available for free and is used as an open source-type software. Since SSL acts as a mature encryption protocol, this means that OpenVPN can run on either a single TCP or UDP port.
VPN Service Provides
In terms of VPN providers, there are certainly many different ones to choose from. Some of these services are available for free, while other providers choose to charge a specific fee for their services. In terms of vpn services, many individuals have gone on record of stating that they prefer IPVanish, which is a service that offers free software, great security, and fast speed.